1 Introduction to Oracle Label Security
Oracle Label Security provides fine-grained access individual table rows. You should understand the benefits of using Oracle Label Security, who has privileges to use it, the duties of Oracle Label Security administrators, and what the components, architecture, and administrative interfaces are for Oracle Label Security. You should also understand how Oracle Label Security works with other Oracle products.
Topics:
About Oracle Label Security
Oracle Label Security enables you to control the display of individual table rows using labels that are assigned to individual table rows and application users.
Oracle Label Security is based on multi-level security (MLS) requirements that are found in government and defense organizations. You can easily restrict sensitive information to only authorized users. Oracle Label Security is based on Oracle Virtual Private Database (VPD). However, unlike VPD, Oracle Label Security provides the access mediation functions, data dictionary tables, and policy based architecture out of the box, eliminating customized coding and providing a consistent label based access control model that can be used by multiple applications. Oracle Label Security policies can be applied to one or more application tables. Oracle Label Security works by comparing the row label with a user's label authorizations. Oracle Label Security software is installed by default, but not automatically enabled. You can easily enable Oracle Label Security in either SQL*Plus or by using the Oracle Database Configuration Assistant (DBCA). To manage Oracle Label Security, you can use either Oracle Enterprise Manager Cloud Control or a set of PL/SQL packages and standalone functions at the command line level. The default administrator for Oracle Label Security is the user LBACSYS. To find information about Oracle Label Security policies, you can query ALL_SA_*, DBA_SA_*, or USER_SA_* data dictionary views.
Benefits of Oracle Label Security
Oracle Label Security provides several benefits.
-
It enables row level data classification and provides out of the box access mediation based on the data classification and the user label authorization or security clearance.
-
It enables you to assign label authorizations or security clearances to both database users and application users.
-
It provides both a graphical user interface and APIs for defining and storing data classification labels and user label authorizations.
-
It integrates with Oracle Database Vault and Oracle Advanced Security Data Redaction, enabling security clearances to be use in both Database Vault command rules and Data Redaction policy definitions.
Who Has Privileges to Use Oracle Label Security?
When you register Oracle Label Security with a database, the registration process creates an administrative user named LBACSYS, who has the LBAC_DBA database role.
You can grant this role to any database user who will be responsible for managing Oracle Label Security policies. In addition, you can grant Oracle Label Security administrators the EXECUTE privilege for the Oracle Label Security packages, and privileges to manage individual Oracle Label Security policies.
Duties of Oracle Label Security Administrators
You can manage the administration of an Oracle Label Security policy by using several privileges.
These privileges are:
-
Package-specific privileges: Most of the Oracle Label Security PL/SQL packages, except for the public
SA_SESSIONandSA_UTLpackages, require theEXECUTEprivilege. -
Role-based privileges: The Oracle Label Security-specific roles are:
-
The
policy_DBArole, which is created and granted to the user when he or she creates a policy. For example, for a policy namedols_hr_pol, the role created is namedols_hr_pol_DBA. This role adds a layer of granularity for access control for your site's Oracle Label Security policies. -
The
LBAC_DBArole, which provides theEXECUTEprivilege for theLBAC_SYSDBApackage. This role is owned by theLBACSYSuser account. TheLBAC_SYSDBApackage enables the user to create, alter, enable, disable, and drop Oracle Label Security policies. This package is a wrapper for theSA_SYSDBApackage.
-
You can use the Oracle Label Security package EXECUTE privilege grants along with grants of the policy_DBA role to achieve additional separation of duty. The packages are categorized based on different tasks. For example, you could grant the EXECUTE privilege on the SA_COMPONENTS and SA_LABEL_ADMIN packages to one user or role to manage label definitions, and then grant EXECUTE on SA_USER_ADMIN to a different user or role to manage user labels and privileges. Both of these users or roles must also be granted the policy_DBA role for the policies for which they are responsible. In this way, different users can be responsible for the management of different aspects of the policies for which they are responsible. For example, user psmith could be responsible for the label definitions of the ols_hr_pol policy, and user tjones could be responsible for the label definitions of the ols_oe_pol policy. However, user psmith cannot modify label definitions for the ols_oe_pol policy, nor can tjones modify the ols_hr_pol policy label definitions.
See Also:
Components of Oracle Label Security
An Oracle Label Security policy has a standard set of components.
These components are as follows:
-
Labels. Labels for data and users, along with authorizations for users and program units, govern access to specified protected objects. Labels are composed of the following:
-
Levels. Levels indicate the type of sensitivity that you want to assign to the row, for example,
SENSITIVEorHIGHLY SENSITIVE. -
Compartments. (Optional) Data can have the same level (Public, Confidential and Secret), but can belong to different projects inside a company, for example ACME Merger and IT Security. Compartments represent the projects in this example, that help define more precise access controls. They are most often used in government environments.
-
Groups. (Optional) Groups identify organizations owning or accessing the data, for example, UK, US, Asia, Europe. Groups are used both in commercial and government environments, and frequently used in place of compartments due to their flexibility.
-
-
Policy. A policy is a name associated with these labels, rules, authorizations, and protected tables.
For example, assume that a user has the SELECT privilege on an application table. As illustrated in Figure 1-1, when the user runs a SELECT statement, Oracle Label Security evaluates each row selected to determine whether the user can access using the privileges and labels assigned to the user and the label on the row. You can configure Oracle Label Security to perform security checks on UPDATE, DELETE, and INSERT statements as well.
Figure 1-1 Oracle Label Security Label-Based Security
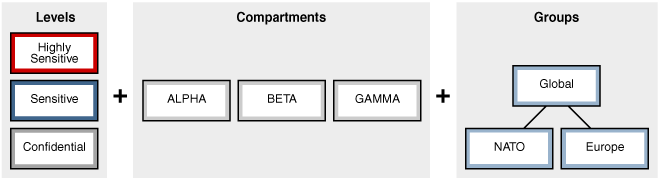
Description of "Figure 1-1 Oracle Label Security Label-Based Security"
Oracle Label Security Architecture
Figure 1-2 shows how data is accessed under Oracle Label Security and the sequence of label security checks.
Figure 1-2 Oracle Label Security Architecture
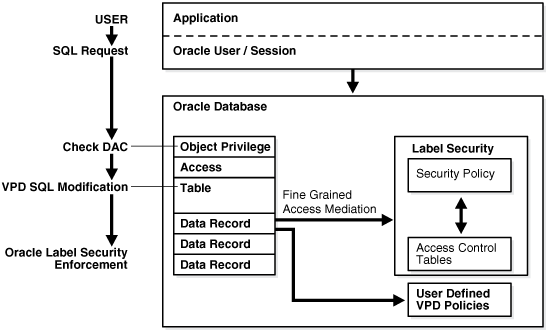
Description of "Figure 1-2 Oracle Label Security Architecture"
In this scenario, the following actions take place:
-
An application user in an Oracle Database session sends a SQL request to query a table.
-
Oracle Database checks the user's data access control (DAC) privileges for performing a
SELECTstatement on the table. -
If the user does have the appropriate privileges, then Oracle Database checks if there are any Oracle Virtual Private Database (VPD) policies attached to the table.
-
Oracle Database then checks if there are any Oracle Label Security policies that are assigned to the table.
-
Oracle Label Security then compares the labels that are assigned to individual rows with the users' label authorizations, allowing or denying access. The session label is based on label authorizations that are assigned to the user.
Oracle Label Security Administrative Interfaces
You can perform Oracle Label Security development and administrative tasks using either of two interfaces.
Topics:
Oracle Label Security Packages
Oracle Label Security packages provide a direct, command-line interface for ease of administration.
Table 1-1 lists the available Oracle Label Security administrative packages.
Table 1-1 Oracle Label Security Administrative Packages
| Package | Purpose |
|---|---|
|
|
To create, alter, and drop Oracle Label Security policies |
|
|
To define the levels, compartments, and groups for the policy |
|
|
To perform standard label policy administrative functions, such as creating labels |
|
|
To apply policies to schemas and tables |
|
|
To manage user authorizations for levels, compartments, and groups, as well as program unit privileges. Also to administer user privileges. See "SA_USER_ADMIN.SET_USER_PRIVS" and "SA_USER_ADMIN.SET_PROG_PRIVS" |
|
|
To set options to audit administrative tasks and use of privileges See "SA_AUDIT_ADMIN Oracle Label Security Auditing PL/SQL Package" |
|
|
To change labels during a during a session within the authorizations set by the administrator |
|
|
A set of utility functions designed for use within PL/SQL programs to return information about the current values of the session security attributes, as numeric label values |
Oracle Enterprise Manager Cloud Control
You can use the Web interface provided by Oracle Enterprise Manager Cloud Control to administer Oracle Label Security.
Figure 1-3 illustrates the Oracle Enterprise Manager interface.
Figure 1-3 Using Enterprise Manager to Configure Oracle Label Security Policies
Description of "Figure 1-3 Using Enterprise Manager to Configure Oracle Label Security Policies"
See Also:
-
"Logging into Cloud Control or SQL*Plus for Oracle Label Security" more information about logging into either Cloud Control or SQL*Plus to administer Oracle Label Security policies
-
Getting Started with Oracle Label Security for details on using Enterprise Manager to administer Oracle Label Security
How Oracle Label Security Works with Other Oracle Products
You can integrate Oracle Label Security with Oracle Internet Directory (OID) and in a multitenant environment.
Topics:
Oracle Label Security Integration with Oracle Internet Directory
Sites that integrate their use of Oracle Label Security with Oracle Internet Directory gain significant efficiencies of label security operation and administration.
You can create and manage directly policies and user authorization profiles in the directory by means of the commands that are described in Command-line Tools for Label Security Using Oracle Internet Directory . Changes are automatically propagated to the associated directories.
A complete introduction to this integration is presented in Oracle Label Security Using Oracle Internet Directory.
Oracle Label Security Integration in a Multitenant Environment
You can use Oracle Label Security in a multitenant environment, in which pluggable databases (PDBs) can be plugged in and out of a multitenent container database (CDB).
Each PDB has its own Oracle Label Security metadata, such as policies, labels, and user authorizations. The LBACSYS schema is a common user schema. See "Enabling the LBACSYS Oracle Label Security User Account" for more information about the LBACSYS account.
Before you plug a PDB into a CDB, if the database does not have Oracle Label Security installed, then ensure that you have run the $ORACLE_HOME/rdbms/admin/catols.sql script on the database. See Oracle Database Administrator's Guide for more information about creating CDBs.
Because Oracle Label Security policies are scoped to individual PDBs, you can create individual policies for each PDB. A policy defined for a PDB can be enforced on the local tables and schema objects contained in the PDB.
You cannot create Oracle Label Security policies in the root. In a single CDB, there can be multiple PDBs, each configured with Oracle Label Security.
If you are configuring Oracle Label Security with Oracle Internet Directory, be aware that the same configuration must be used throughout with all PDBs contained in the CDB. You can determine if your database is configured for Oracle Internet Directory by querying the DBA_OLS_STATUS data dictionary view as follows from within any PDB:
SELECT STATUS FROM DBA_OLS_STATUS WHERE NAME = 'OLS_DIRECTORY_STATUS';
If it returns TRUE, then Oracle Label Security is Internet Directory-enabled. Otherwise, it returns FALSE.
See Also:
-
Oracle Database Security Guide for information on how the multitenant architecture affects privileges
-
"Oracle Label Security Integration with Oracle Internet Directory" for information about Internet Directory-enabled Oracle Label Security